Detecting Bombs and Weapons with WiFi
Rutgers University researchers have developed a WiFi-based system for detecting dangerous objects that is faster and less expensive than scanners seen in airports and other venues.
November 16, 2018
|
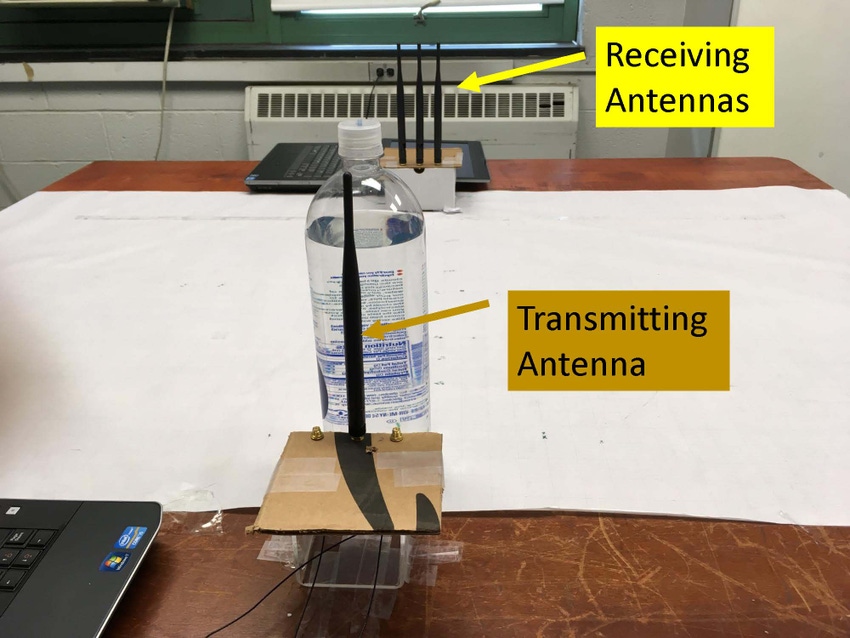
Here is one of the experimental setups for object material identification and risk level estimation. (Image source: Rutgers University) |
Our world is literally awash in electromagnetic waves—most recently, WiFi and cellular communications that have enabled the mobile revolution. Because these waves are already there, is there some other way that they might be used? Some kind of free fringe benefit that could take advantage of their nearly ubiquitous presence?
After all, electromagnetic waves can be used for other things. For example, careful analysis of reflected energy emanating from a monitored region can tell us if certain types of objects have entered that space. This is the principle behind radar, which has proven to be a tremendously useful tool.
Radio and TV waves encompass too much distance relative to the strength of their signals for this kind of use. But perhaps it might be possible to use WiFi signals to learn something about what's going on within the limited space that they are addressing.
RELATED ARTICLES:
This is the thinking behind a new "suspicious object detection system" developed by a team of researchers at the Wireless Information Network Lab (WINLAB) at Rutgers University. The system employs a sophisticated analysis algorithm that scrutinizes ordinary WiFi signals to determine the presence of dangerous objects concealed in backpacks or luggage.
So how well does it work? According to the paper published in the proceedings of the 2018 IEEE Conference on Communications and Network Security, "Extensive experiments with 15 representative objects, six types of bags/boxes are conducted over a six-month period. We show that our system can achieve over 95% and 90% accuracy for identifying the suspicious object and determining its material type and achieve an average error of 16 ml and 0.5 cm for estimating liquid volume and metal object’s shape."
This kind of activity recognition could, for example, tell an observer if you were walking around inside your home or exercising, or cooking, or sitting. Other applications under investigation include vital signs monitoring. Finger gestures can also be monitored using this approach.
According to study co-author Yingying Chen, the system—which utilizes existing WiFi-enabled hardware, such as cell phones, tablets, or laptops, and requires only the installation of specialized software and possibly a modified antenna—has several advantages over the kinds of scanners we see in airports today. It is significantly less expensive, can be set up quickly for temporary use, doesn't require line of sight, and can scan a wide section of a crowd at once—allowing for much faster and less obtrusive screening.
|
The researchers used a two-step material identification method based on CSI complex and CSI complex difference to detect liquids and metals. (Image source: Rutgers University) |
Chen said her group began the research by observing the channel state information (CSI) for the broader purpose of activity recognition. CSI represents the collective channel properties of a communication link. From these properties, one can gain a sense of how a signal propagates from the transmitter to the receiver and represents the combined effect of, for example, scattering, fading, and power decay with distance.
From there, the idea emerged that it might be possible to see concealed objects, as the wavelength of WiFi signals (roughly 12.5 cm) allows them to pass through the kinds of materials from which most luggage and backpacks are made.
Because of the relatively low signal to noise ratio, a two-pass method—utilizing two different devices (e.g., laptops) with slightly different antenna configurations—is required to obtain sufficient accuracy. First, a calibration is performed with each data sample, followed by elaborate signal processing steps that include "correction of the CSI phase drifting and reconstruction of the CSI complex including amplitude and phase correction."
The first analysis step, called the "material classification," analyzes signal refraction data collected by a device equipped with two antennas, spaced a nominal distance apart, to detect the presence of a suspicious object—either a liquid or a metal. The second step, "object risk estimation," uses signal reflection data obtained from a device with two closely spaced antennas to determine either the size and shape of the metal object or the volume of the liquid.
But Chen does not yet suggest replacing the more highly effective and more costly radar and X-ray installations currently deployed in airports, military bases, and power plants. However, she added that the WINLAB system could be very useful in other areas where cost is an issue but some level of security is highly desirable, such as sporting events, concerts, festivals, and even small businesses.
She also suggested that the system could be deployed in "smart robots that could walk through the crowd or in drones that could fly over at low altitude.” In addition, the technology could be applied to a kind of crowd-sourced security, where attendees could run an app on their cell phones that could notify them or perhaps feed directly to law enforcement if a suspicious item is detected.
RP Siegel, PE, has a master's degree in mechanical engineering and worked for 20 years in R&D at Xerox Corp. An inventor with 50 patents and now a full-time writer, RP finds his primary interest at the intersection of technology and society. His work has appeared in multiple consumer and industry outlets, and he also co-authored the eco-thriller Vapor Trails.
About the Author(s)
You May Also Like






