3D Printing Has an Urgent Need for Cybersecurity
It's not just about hackers stealing designs. New research shows that 3D-printed products can be tampered with to create counterfeits and undetectable, devastating flaws.
March 17, 2017
|
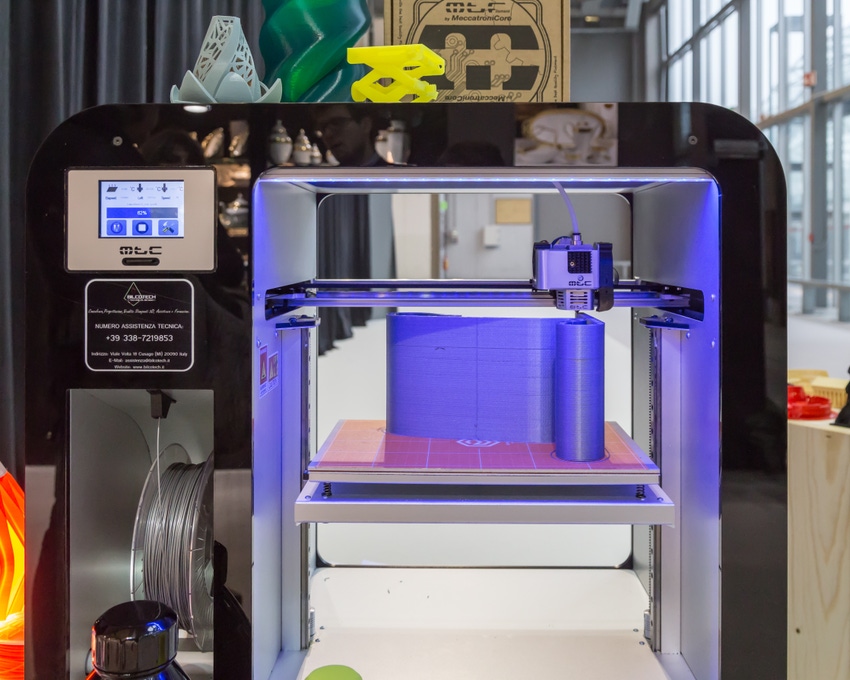
Whether intentionally or unintentionally, 3D printers can be tricked into creating components with defects that standard tests cannot detect. (Image source: New York University) |
In the race to adopt new 3D printing and additive manufacturing (AM) technologies, engineers and manufacturers are overlooking a key element – cybersecurity.
According to a new paper, “Manufacturing and Security Challenges in 3D Printing”, written by researchers at New York University's Tandon School of Engineering and published in the May 2016 issue of the journal JOM, The Journal of The Minerals, Metals & Materials Society (TMS), 3D printing carries cybersecurity vulnerabilities that can lead to potentially dangerous, undetectable defects as well as opening the door for counterfeit products.
Nikhil Gupta, an associate professor of mechanical and aerospace engineering at NYU Tandon, and one of the co-authors of the paper, told Design News that the cybersecurity risks that come with AM are far more significant that common threats we hear about today. “The number one problem is you are creating a physical object that will be used in a system,” Gupta said. “This is not like a stolen credit card number that you can change quickly to avoid damage. In this case the product is created and being used in a system.”
Imagine a 3D-printed shaft breaking while someone is driving at high speed and you start to understand Gupta's concerns. “Our emphasis in this paper was to show there could be certain small defects in materials, so small that common detection techniques would miss them, but they compromise the properties of these components,” he said. “Many people have shown [3D printers] can be hacked. As a materials scientist my emphasis was to show these tiny defects can be included that would comprise the integrity of the materials used.”
Gupta and his team conducted their research in two parts. In the first they examined the effect of printing orientation on products' structural integrity. Since CAD files do not specify printer head orientation, the researchers wanted to see if any change in orientation would have a measurable impact.
|
NYU Tandon researchers printed test products in three orientations and found that altering the orientation of a 3D print could have a significant impact on the material strength. (Image source: New York University) |
Test products with the same geometry were printed to the ASTM D638 standard, but at three different orientations. The researchers found that altering orientation could result in a significant loss of tensile strength. Of the three orientations tested they found that one (a 45-degree orientation) was up to 30% stronger than the other two orientations. “Thus, if the original model is intended to be oriented at 45 direction for printing, a change in the printing direction can significantly lower the strength and modulus, making the part underperform compared to the design conditions,” according to the paper.
In the second part of their study, the researchers deliberately introduced sub-millimeter defects that could result in product failure between printed layers of products printed to the ASTM E8 standard. When the printed parts were quality checked using a combination of ultrasonic C-scan and finite element analysis (FEA) the defects were undetectable. What they discovered is that 3D printers are capable of either being intentionally or inadvertently instructed to create defects in products – meaning hackers could intentionally alter a print to ill effects or manufacturers could unintentionally do it themselves by adopting practices that result in products being printed in less than ideal conditions. According to the paper, these attacks could take the same form as hardware trojan attacks that go after the integrated circuit (IC) process chain, but would require very different defenses because of the small-batch nature of AM.
“These features may be introduced by several reasons which include undesired features in the STL file due to the gaps caused by the tessellation process, printer skipping a print step due to mechanical issues, or a hacker intentionally introducing a sub-detection limit feature to compromise the product quality,” according to the paper.
Explore The 3D Printing Revolution |
Prior research, including as a study conducted by researchers at the University of California, Irvine as well as separate research done by the University at Buffalo have shown 3D printers can be hacked through various methods (including recording the acoustic waves made by the printer) to steal or replicate the design files the printer is using. For Gupta this, combined with his own research, represents a significant danger for AM. “If someone steals CAD files or files used for 3D printing there's nothing that stops people from reprinting those parts in very high quality,” Gupta said. “They can create a product as good as the original.
“The problem comes from two sides: There may be malicious persons or someone may counterfeit a product. And owners of the IP can't distinguish original from knock off.”
Securing 3D Printing
So what then are the solutions? Gupta said there is the possibility of using and creating new a better materials. However he said, “There are printing techniques that only work with certain materials. At this point AM is limited to using a certain variety of materials, so you have to look at a combination of materials and printing to tackle the problem.”
What about new detection methods? It's possible, but it might not be the most cost-effective solution. “ There are these methods that are already in line,” Gupta said. “Testing every product for every possibility of defect is very expensive. You can use something like a CT scan that will give more defects, but it's more expensive because of time and cost constraints.
“Testing methods we have now are optimized for traditional manufacturing methods so what we are thinking is these methods have to evolve and keep pace with 3D printing. There is no one solution that will work in all cases. It depends on how critical the part is and what kind of performance compromise can happen. So there has to be a threat analysis before you can modify the testing.”
READ MORE ARTICLES ON 3D PRINTING:
For Gupta everyone along the complex supply chain, from the 3D printer manufacturers themselves to the design engineers that use them, all the way to the manufacturers, are going to have to take some role in addressing these cyber threats.
Gupta himself has co-founded a startup, 3DP Security, focused on identifying and addressing cybersecurity threats associated with 3D printing. The company has identified four key solution areas: embedded tracking to ensure CAD files are not stolen; automatic dimensional control to ensure optimized printing; CAD modeling strategies; and microstructure tagging.
Gupta places the most emphasis on these last two. The idea is that new security features could be embedded into CAD files or the printed products themselves in order to deter counterfeiting and prevent knock-offs or components that have been maliciously tampered with from being used. “We have designed a set of features you can put into a CAD file that will print the part only under a very specific set of conditions,” Gupta said. “If somebody steals that file then the part they create will be defective. So there will be a very clear point of distinguishing a counterfeit from a genuine product.” He also suggested expanding the same technology into creating ID codes (barcodes or QR codes) that can be printed in the parts. “Those codes can be scanned in very specific conditions and you can find out whether the part is genuine.”
Gupta added there is also the possibility of creating materials which have very specific properties like tracer elements so you can use spectroscopy to determine if the right material has been used or not to tell if a part is counterfeit.
All of this is not to say these cybersecurity issues have come out of intentional oversight. Gupta chalks it up to the pace of innovation. “A lot of people didn't have time to think about this problem because these printers are now everywhere,” he said. “The wave came so fast that a lot of companies had to jump into it.”
For Gupta and his team what it may come down to is creating a whole new set of AM standards, or at least augmenting those already in place.
“Protection of these [CAD] files is more important in this field and a lot of people didn't realize because it came into their lives so fast,” Gupta said. “But it's going to catch up. I have no doubt that within a year or two this is going to be among the top priorities for companies that are now getting into AM.”
Chris Wiltz is the Managing Editor of Design News.
About the Author(s)
You May Also Like






