Cloud-based solutions often cost less and require less time in purchasing, installing, configuring, and maintaining compared with onsite PCs and software.
Many OEM manufacturers would love to reduce downtime and track quality with web-based dashboards and a smart phone app, but the notion of doing so using a cloud-based solution often rubs them the wrong way.
There’s a common misconception in the market that cloud-based solutions are less reliable and secure than traditional in-house solutions. That’s hardly the case. By leveraging the software, hardware, and expertise of a turnkey Industrial Internet of Things (IIoT) provider, you can have actionable business intelligence at your fingertips for a fraction of the time and cost of purchasing, installing, configuring, and maintaining onsite PCs and software, and when done properly, hosted IIoT solutions are just as secure as your online checking account. In fact, a hosted solution may actually be more secure than your onsite PC.
Security breaches typically occur when an employee opens an email, browses the internet, plugs in a USB device, or neglects software security patches. These issues are far more likely on a production floor PC than on a well-maintained tier level 3 data center.
Your company policies may prohibit these security lapses, but that doesn’t mean they never happen. As cybersecurity expert and former White House CIO Theresa Payton often points out in her presentations, the biggest security threat to your organization may be hardworking employees who inadvertently expose data in their drive to get the job done. “Zero risk does not exist – make sure managed risk does,” Payton has said.
Do Your Due Diligence on Security
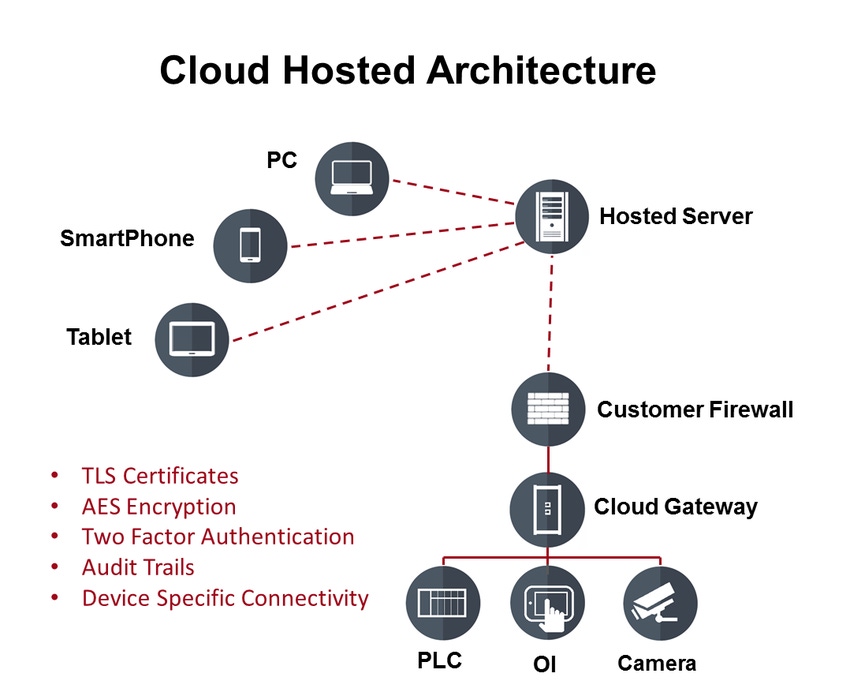
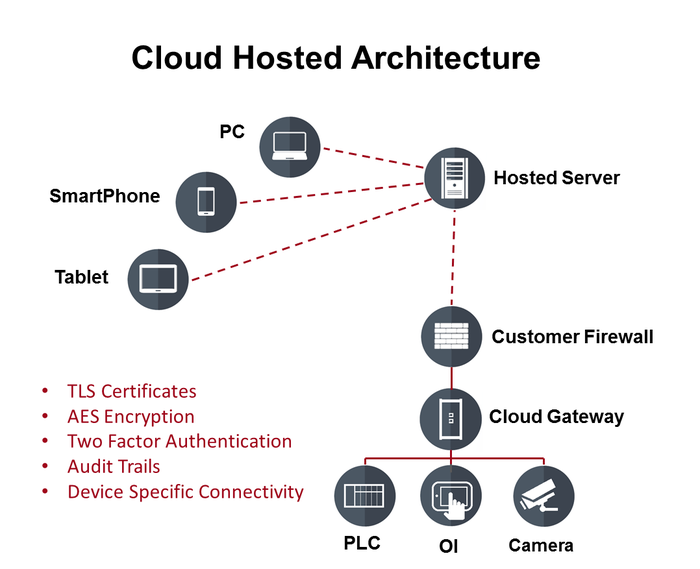
Not all hosted solutions are alike of course, so it is important to find out where the system is hosted and what security features are included. At a minimum you should look for security certificates, data encryption, and two-factor authentication. Audit trails should be considered if you want to track who is accessing your data and how often.
Servers should be located in a secure data center with backup power and automatic backups. If remote hosting is absolutely out of the question, your IIoT provider may be willing to install the hosted servers on your site. This adds cost but can still save time and money when compared to the traditional do-it-yourself approach.
READ MORE ARTICLES ON CLOUD-BASED SOLUTIONS:
When online banking and online credit card purchases were first introduced, most people were just as skeptical as the “Never Clouders” are today. Over time the convenience of online banking became so commonplace that the task of handwriting and mailing checks every month began to seem absurdly tedious and outdated. Similarly, the business benefits of having actionable intelligence at your fingertips through cloud-hosted solutions already outweighs the perceived risks for a broad range of industrial manufacturers in a broad range of industries.
|
Tom Craven is vice president of product strategy at RRAMAC Connected Systems. Prior to RRAMAC, Craven was the operator interface product manager at GE Intelligent Platforms. He has extensive experience working as a sales and applications engineer and is passionate about exploring new ways to bring cloud-based analytics to equipment manufacturers.
About the Author(s)
You May Also Like




