Design Software
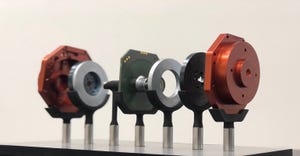
Smart grid runs on smart IoT product design, engineering, manufacturing
Sponsored Content
The Crucial Role of ODMs in Overcoming IoT Project ChallengesThe Crucial Role of ODMs in Overcoming IoT Project Challenges
How partnering with an original design manufacturer (ODM) can accelerate product time to market, broaden access to skills and expertise, and streamline certification processes.
Sign up for the Design News Daily newsletter.