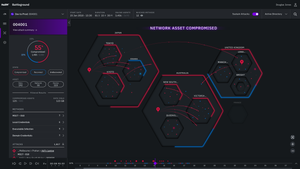
Cybersecurity
Medical device software development.svg?width=700&auto=webp&quality=80&disable=upscale)
CybersecurityPro Tips for Medical Device Software DevelopersPro Tips for Medical Device Software Developers
Hear expert advice on how to innovate while staying ahead of cybersecurity threats in a free webinar hosted by MD+DI and Qmed+.
Sign up for the Design News Daily newsletter.