Communication gateways improve cybersecurity as they help serial-based intelligent electronic devices (IEDs) communicate with Ethernet-based networks.
March 23, 2022

Felipe Sabino Costa, LATAM industrial cybersecurity expert at Moxa
Because of a significant surge in distributed energy resources (DERs) and energy storage systems, along with the upward trend of unmanned substations, power grids have become a lot more complex. So far, DERs are having the biggest impact on power grids because of their intermittent energy production. At times, they generate too much power; other times, their output is too low. These fluctuations make the grid unreliable.
For this reason, engineers in substation control centers find it increasingly difficult to manage the dispatch of power in real-time. To address these instabilities in power grids, digital substations, which provide stability and flexibility regarding power supply, increasingly play an important role in power transmissions. However, converting all substations to digital at once is not so straightforward because of limited budgets to retrofit a large number of serial-based legacy devices.
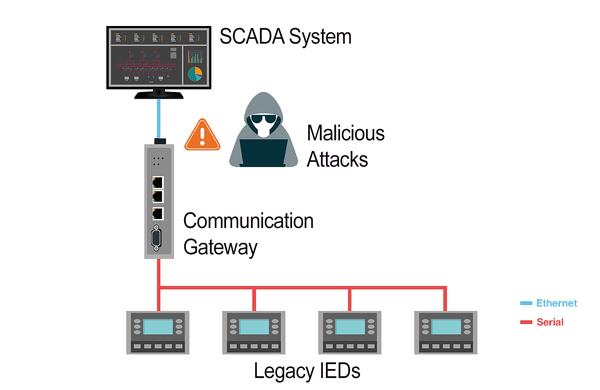
Communication gateways can help overcome these concerns as they help serial-based intelligent electronic devices (IEDs) communicate with Ethernet-based networks. They are also a cost-effective solution compared to computing platforms. With the serial-to-Ethernet problem solved, however, another issue raises its head: cyberattacks always pose enormous threats to Ethernet-based networks, putting cybersecurity in retrofit power substations at the forefront.
Cybersecurity for Substation Automation Systems
Substation protection and control systems manage critical power operations through communication protocols. In substation retrofitting projects, communication gateways act as data concentrators, managing the large numbers of legacy IEDs. Despite their significantly important role, communication gateways rarely incorporate adequate security measures. Therefore, a high risk exists that malicious attackers can easily access legacy IEDs through these gateways to cause system downtime, power outages, and damage to critical equipment, resulting in huge financial losses. What’s even worse, people’s lives can also be in danger.
The IEC 62443 standard has become one of the most popular cybersecurity standards for industrial automation and control systems. For specified critical power automation systems, also consider a specified power standard such as IEC 62351. When incorporating the acknowledged technologies of both standards, operators need to consider methods that can protect their critical data and track their network security status.
Encrypt Your Critical Data to Reduce Cyberattacks
Once hackers invade a substation network, they can easily capture data and learn a lot about network communication behavior. What’s more, they can easily cause havoc by sending the wrong command to control the IEDs. To counteract these types of malicious activities, communication gateways must encrypt data for communication protocols such as DNP3 TCP and IEC 61850 MMS.
Monitoring the Security Status of Networks
For monitoring and controlling IEDs in refurbished substations, it is critical to make the network infrastructure more secure. The status of network devices, such as switches, IEDs, and communication gateways must always be monitored. For example, if the links of an Ethernet port of a network device are down or malicious behavior is detected, the gateway will send an alarm message to the information system immediately. When the information system receives the alarm, engineers can handle this problem in a timely manner.
Secure IEC 61850 Substation Gateways
Advanced IEC 61850 gateways secure devices from configuration to daily maintenance. They also enhance communication security, ramping up network security for retrofitted substations.
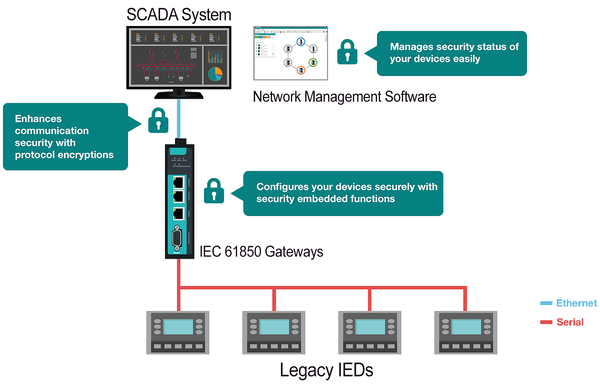
Substations are exposed to potential threats once they connect to networks. Thus, all networking nodes need to be protected from intruders. Based on IEC 62443 and NERC CIP guidelines, IEC 61850 gateways provide multiple security functions to ensure a device is secure in the initial configuration process.
Password-cracking defense: Using default passwords for convenience is not an option anymore. IEC 61850 gateways have a password policy that encourages the use of stronger passwords to avoid unwanted access.
Sniffer and data breaches protection: Using plain text for device configuration can be dangerous. IEC 61850 gateways provide SSL/TLS to encrypt critical data during the configuration process.
Configuration file and program tampering resistance: When exporting configuration files for backup, IEC 61850 gateways will encrypt the file to enhance a file’s integrity.
DDoS defense with built-in detection capabilities of suspicious activities: DDoS attacks are usually carried out by occupying network bandwidth or attacking the resources of networking devices. IEC 61850 gateways help detect abnormal packets and send alerts for instant response.
Enhance Communication Security With Protocol Encryptions
If data communications are not encrypted, then hackers can capture plain text data easily. From the plain text data, hackers can figure out how to control IEDs and subsequently send out a fake control command to them, which could endanger substation operations. IEC 61850 gateways support TLS v1.2, which secures data transmission between communication gateways and a power SCADA system, using standard communication protocols such as IEC 61850 MMS and DNP3 TCP.
Manage Security Status of Your Devices Easily
Security is not a one-time event, but a journey that requires constant monitoring of device security status in daily operations. IEC 61850 gateways should support network management software that provides intuitive network topology to help users easily check device status. Moreover, the users should be able to monitor user-defined security events and bring violations to the administrator’s attention. This way, engineers can easily check and ensure IEC 61850 gateways operate at the accepted security level.
In addition to enhancing communication security, a properly equipped IEC 61850 gateway should also come with functions that make configuration and troubleshooting efficient. An industrial-grade design is also critical to ensure operational reliability for demanding substation retrofits projects.
Felipe Sabino Costa is an electrical and electronics engineer and an official ISA/IEC-62443 industrial cybersecurity instructor for the International Society of Automation. He is a LATAM Industrial Cybersecurity (IACS) Expert, an international speaker, and an author of books and white papers. With over 15 years inside the industrial sector dealing with a wide array of technologies and products, he is dedicated to developing mission-critical solutions that include cybersecurity by design.
You May Also Like



