News
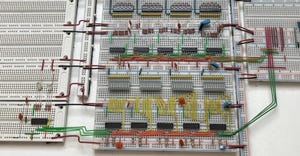
Rust embedded software
Embedded Systems
5 Rust Runtimes Every Embedded Developer Needs to Know5 Rust Runtimes Every Embedded Developer Needs to Know
The fast and efficient Rust can be used for embedded software applications, and these runtimes could help.
Sign up for the Design News Daily newsletter.









.jpg?width=300&auto=webp&quality=80&disable=upscale)